Cybersecurity: Cloud Computing Products
Audit snapshot
What we examined
We examined the effectiveness of agencies' Microsoft 365 cloud-based identity and device management controls.
We selected a range of agencies, including government departments, a local council, a water authority, a health service and other entities, to assess their approaches to cybersecurity. We did not examine Cenitex’s and the Department of Government Services’ controls.
Why this is important
Cybersecurity threats in Victoria are real and growing.
The Department of Premier and Cabinet reported that 90 per cent of Victorian Government agencies experienced cybersecurity incidents last year.
Successful attacks on Victorian Government agencies have seriously disrupted critical services.
It is important that agencies have strong cybersecurity controls to reduce the risk of this happening again.
This includes making sure:
- their identity and device controls are effective
- they only allow authorised users and approved devices access to sensitive information.
What we concluded
The audited agencies’ Microsoft 365 cloud-based identity and device controls are not fully effective. They can do more to improve their cybersecurity.
The public sector does not use its size and economy of scale to address cybersecurity risks in a coordinated way.
Agencies have recognised the need to establish a whole-of-government approach. But they need to do more to improve cybersecurity for the entire sector.
What we recommended
We made 2 recommendations to the newly formed Department of Government Services and one recommendation to the Office of the Victorian Information Commissioner to lead a whole-of-government approach to improve the public sector’s cybersecurity.
We made 4 recommendations to all the agencies we audited to address control weaknesses and improve their cybersecurity.
We also made one recommendation about improving agencies’ oversight of the cybersecurity services they outsource.
Video presentation
Key facts
Note: *Multi-factor authentication (MFA) is a control that requires users to verify their identity using at least 2 methods before they can access an agency's systems or documents.
Source: VAGO based on agencies' information.
Our recommendations
We made 7 recommendations to address 3 key findings. The relevant agencies have accepted the recommendations in full or in principle or with qualifications. While our recommendations are directed to audited agencies, we expect all Victorian public sector agencies to implement them where appropriate.
| Key issues and corresponding recommendations | Agency response(s) | |||||
|---|---|---|---|---|---|---|
| Issue: The public sector lacks a coordinated approach to address cybersecurity risks | ||||||
|
Department of Government Services and Office of the Victorian Information Commissioner |
1 |
Work together, in consultation with other relevant agencies, to issue non-overlapping guidance that:
The guidance should mandate:
This mandate should apply to all classes of identities and devices used to access public sector resources, including but not limited to personal computers, mobile devices, guest users, ordinary users, privileged users, service accounts and non human identities. Agencies should report their compliance against the issued guidance to their accountable risk owners and audit and risk committees at least annually (see Section 3). |
Accepted by the Department of Government Services Accepted with qualifications by the Office of the Victorian Information Commissioner |
|||
|
Department of Government Services |
2 |
Extends the cyber hubs and the security operation centres to:
|
Accepted in principle |
|||
|
All audited agencies that are not using a security operation centre |
3 |
Complete an independent (internal or external) risk assessment to inform whether they need a security operation centre to improve their cybersecurity and report the results of this assessment to their accountable officer and audit and risk committee. The risk assessment should:
|
Accepted by all applicable agencies |
|||
| Issue: Audited agencies do not have fully effective Microsoft 365 cloud-based identity and device controls | ||||||
|
All audited agencies |
4 |
Address the technical compliance control configuration weaknesses we detailed in each agency's management letter (see Section 2). |
Accepted in principle by the Department of Education Accepted by all other applicable agencies |
|||
|
5 |
Report the following to accountable risk owners at least quarterly:
|
Accepted by all applicable agencies |
||||
| 6 | Ensure accountable risk owners document their risk acceptance for controls marked as risk accepted, resolved via third-party solutions or alternative mitigations (see Section 2). | Accepted by all applicable agencies | ||||
| Issue: Audited agencies insufficiently oversee cybersecurity services delivered by third-party providers | ||||||
|
All audited agencies who use third-party services |
7 |
Oversee and ensure that:
|
Accepted by all applicable agencies |
|||
What we found
This section summarises our key findings. Sections 2 and 3 detail our complete findings, including supporting evidence.
In this report we do not specify which findings relate to which agency given the sensitive nature of the weaknesses we observed. But we have given each audited agency a detailed report about their own control deficiencies.
When reaching our conclusions, we consulted with the audited agencies and considered their views. The agencies’ full responses are in Appendix A.
Why cybersecurity is important
A successful cyber attack can harm the community and cause severe damage.
This is because an attack can:
- cause personal data breaches
- disrupt communication networks
- shut down water, health and other critical facilities.
The Victorian Government considers cybersecurity to be one of the top 10 risks for the state.
It became even more important for organisations to have effective cybersecurity controls when Victorians started working from home during the COVID-19 pandemic.
This is because staff often use their own internet service to connect to agencies' networks.
Our key findings
Our findings fall into 3 key areas:
|
1 |
Overall, audited agencies do not have fully effective Microsoft 365 cloud-based identity and device controls. |
|
2 |
Not all audited agencies properly understand and oversee cybersecurity services delivered by third-party providers. |
|
3 |
The public sector does not use its size and economy of scale to address cybersecurity risks in a coordinated way. |
Key finding 1: Overall, audited agencies do not have fully effective Microsoft 365 cloud-based identity and device controls
Why effective identity and device controls are important
Identity and device controls are the first 2 pillars of the zero trust model. These cybersecurity controls help agencies:
- make sure only authorised users and approved devices can access sensitive information
- comply with recommended security frameworks and standards.
The zero trust model’s 6 pillars
Identities, devices, applications, data, infrastructure and networks are 6 foundational elements, or pillars, that make up modern information technology (IT) operations.
The zero trust model is a high-level strategy. It assumes that users, devices and services attempting to access resources, even from inside the network, cannot automatically be trusted.
Effective identity and device controls
We developed a list of best-practice compliance controls for identity and devices. We used this list to assess the maturity of agencies’ cybersecurity controls.
The list does not include all applicable identity and device controls. We selected controls based on relevant frameworks and standards, which Section 1 details.
The list is a good starting reference for agencies to understand what best-practice compliance looks like. It can help agencies identify gaps in how they manage their identity and device controls.
Identity controls
We assessed 33 identity controls. None of the agencies have fully implemented all these controls. Specifically:
|
We assessed if agencies … |
Out of 8 agencies we looked at, we found … |
|---|---|
|
have a centralised identity and access management (IAM) system. |
|
|
have controls for managing privileged access. |
|
|
require strong user authentication methods. |
|
|
set up conditional access policies for identity. |
|
Privileged access management
Agencies can give some users access to more functions than standard users, such as accessing, modifying or deleting sensitive information as well as making changes to servers, devices and user accounts.
MFA
MFA is a control that requires users to verify their identity using at least 2 methods before they can access an agency’s systems or documents.
Passwordless authentication
Passwordless authentication lets a user access an application or IT system without entering a password. Instead, the user may log in with passwordless technology, such as biometrics.
This reduces the risk of people relying on remembering passwords to access systems.
Conditional access policies
Agencies can implement conditional access policies to require a user to complete an action if they want to access their networks.
Device controls
We assessed 22 device controls. None of the agencies have implemented all these controls. Specifically:
|
We assessed if agencies … |
Out of 8 agencies we looked at, we found … |
|---|---|
|
set up conditional access policies for devices. |
|
|
have and use cybersecurity solutions. |
|
|
define and implement configuration policies that include:
|
|
Cybersecurity solution
Modern cybersecurity solutions use technology such as threat and artificial intelligence to analyse user behaviours and other signals. These solutions can be used to detect and respond to threats.
A native cybersecurity solution is one from the cybersecurity platform provider, such as Microsoft.
Security configuration baseline
A security configuration baseline is the recommended settings that an agency can use to set up its devices.
Compliance policy
A compliance policy is a set of rules that a device must comply with. For example, an agency may require devices to have antivirus software.
Impact of ineffective identity and device controls
Without effective identity and device controls agencies are more susceptible to cyber attacks.
This is because agencies cannot stop malicious users from using unsecured accounts and noncompliant devices to access their networks.
Reporting on compliance and security posture
All audited agencies have assigned risk owners for their cybersecurity risks and report emerging risks to their relevant committees.
|
We assessed if agencies report their … |
Out of 8 agencies we looked at, we found … |
|---|---|
|
compliance against the Victorian Protective Data Security Standards. |
|
|
Microsoft Secure Scores (secure scores) to accountable risk owners. |
|
An agency’s secure score indicates its security posture in the Microsoft 365 cloud environment.
Secure scores are automatically calculated using monitoring technology that scans an agency’s environment. But if an agency uses a third-party solution or an alternative mitigation, a secure score may not accurately reflect if the agency has adequately set up a control.
Of the 8 audited agencies, each agency implemented an average of 180 out of 1,072 (17 per cent) controls using third-party solutions and alternative mitigations.
This means that:
- the reported secure scores may not accurately reflect an agency’s true security posture
- agencies cannot solely rely on their secure scores to monitor their security posture. Agencies need to confirm if their controls that use third-party solutions and alternative mitigations have been set up properly.
Key finding 2: Not all audited agencies properly understand and oversee cybersecurity services delivered by third-party providers
Why it is important
An agency can use a third-party service provider to manage their cybersecurity services.
But the agency is accountable for its overall cybersecurity risks. This is because an agency cannot delegate its accountability to a third-party provider.
Being accountable for cybersecurity risks means that an agency should:
- be clear about the roles and responsibilities it has under:
- shared service arrangements
- managed service arrangements
- regularly review and ensure the controls implemented in both arrangements meet the agency’s requirements and address its cybersecurity risks.
Shared service arrangement
Under a shared service arrangement, the service provider determines and implements controls. An agency needs to assess if the controls meet its requirements before entering the engagement.
Managed service arrangement
Under a managed service arrangement, the agency determines and oversees the controls. The service provider is responsible for implementing them.
Cenitex-managed shared services and products
Cenitex manages a suite of Microsoft 365 products. Many government agencies use and share these products and services.
Cenitex can play different roles depending on how agencies want to engage with it.
When Cenitex is the cloud service provider under a shared service arrangement:
- Cenitex is the owner of the shared products and services and is responsible for determining and configuring cybersecurity controls for the Microsoft 365 tenancy
- agencies are users, not owners, of these products and therefore are only responsible for their data in the Microsoft 365 tenancy.
Agencies are not clear about their security roles and responsibilities under the shared service arrangement.
For example, some agencies who are part of the shared tenancy think they are the owners of the tenancy and should be able to determine and configure cybersecurity controls.
Agencies, as users of the tenancy, should:
- periodically review if controls for Cenitex’s Microsoft 365 tenancy meet their cybersecurity requirements
- identify if they need to implement additional controls to address any identified gaps and assess if:
- these controls can be implemented by Cenitex
- agencies need to set up controls of their own outside of the tenancy to mitigate their cybersecurity risks.
If these options are not possible, agencies should consider other suitable arrangements.
Microsoft 365 tenancy
A Microsoft 365 tenancy is a dedicated environment within the Microsoft 365 cloud. It provides a range of services from Microsoft.
When an agency buys a Microsoft 365 subscription, it is allocated to a tenancy. Agencies can share a tenancy.
Impact of unclear roles and insufficient oversight
There could be potential gaps in agencies’ cybersecurity controls because they:
- have an unclear understanding of their roles
- do not sufficiently oversee the shared services.
Key finding 3: The public sector does not use its size and economy of scale to address cybersecurity risks in a coordinated way
Why a coordinated approach is important
Audited agencies have different levels of maturity for cloud-based identity and device controls.
Agencies recognise that:
- cybersecurity skills are distinct from general IT skills
- preventing, detecting and responding to cyber attacks requires a multidisciplinary team with expertise across different security functions.
As agencies move away from on-premises computing to cloud computing platforms, they are also increasingly changing their control configurations from agency-specific settings to universal uniformed ones. This means that the identity and device control options for agencies will become well defined and near identical.
Agencies do not always have the resources to establish cybersecurity teams with up to date knowledge and skills. But they could benefit from a whole-of-government approach to implement these controls to improve their cybersecurity.
Proposed cyber operating model
In November 2020, the Department of Premier and Cabinet established Digital Victoria to support digital transformation across the Victorian Government. Digital Victoria moved to the Department of Government Services on 1 January 2023.
Digital Victoria aims to guide and support the public sector to work in a more collaborative way.
Victoria's Cyber Strategy 2021 and its 2021–2023 mission delivery plans recognise the need to build a cyber hubs model to improve the public sector's governance, technology and how it manages resources.
As part of the work to deliver Victoria's Cyber Strategy 2021, Digital Victoria asked agencies to voluntarily share their Microsoft Secure Score data so it could:
- analyse agencies' cybersecurity
- identify which agencies need extra support
- identify what areas agencies need further training in.
However, not all agencies agreed to share their data. This is because Digital Victoria has no legal authority to issue mandatory guidance and request information.
As a result, although 150 agencies agreed to participate in the program, Digital Victoria was only able to analyse the data from 40 agencies who shared their data.
This means Digital Victoria:
- does not have full visibility of agencies' cybersecurity data
- cannot identify systemic issues or concerns across the sector.
This may affect Digital Victoria's ability to deliver the whole-of-government cyber operating model.
Using centralised SOCs
We found that not all agencies use centralised security operation centres (SOCs).
A SOC is an in-house or outsourced team of IT security professionals that monitors an agency's IT systems 24/7 to:
- detect cybersecurity risks in real time
- respond to risks of attacks as quickly and effectively as possible.
The health sector set up its SOC in 2020. This is a good example of agencies detecting and responding to cybersecurity risks using a centralised solution.
Under the 2021–2023 mission delivery plans, Digital Victoria aims to set up centralised SOCs for agencies, including government departments and entities and local government authorities.
However, the current SOC arrangements do not provide services for agencies to protect against cyber attacks. This means that individual agencies are delivering this function independently.
It is often challenging for individual agencies to have the necessary resources and scale to establish cybersecurity teams with up-to-date knowledge and skills.
This gap in the arrangements can expose agencies to high cybersecurity risks.
Impact of not having a coordinated approach
There are over 3,000 entities that deliver services to the public.
Without a coordinated approach, many agencies are duplicating their efforts and not using the public sector’s economy of scale to efficiently manage cybersecurity risks.
1. Audit context
Cyber attacks
Impact of cyber attacks
Public sector agencies are constantly at risk of cyber attacks.
Microsoft reports and analyses 43 trillion threat signals for its cloud computing products every day.
Cyber attacks can:
- cause data breaches of:
- personal information
- confidential information about organisations
- interrupt the availability of IT systems, which can lead to agencies not being able to provide critical services.
Figure 1 shows a number of recent high-profile cyber attacks that impacted critical infrastructure.
Figure 1: Recent high-profile cyber attacks that impacted critical infrastructure
|
2019 Victorian hospital cyber attacks |
In September 2019 multiple hospitals in Victoria experienced a cyber attack. Malicious users installed software that made booking systems unusable for more than 24 hours. While no patient information was leaked, it delayed surgeries. |
|
2021 USA Colonial Pipeline shutdown |
In 2021 malicious users accessed America’s largest oil pipeline using a staff member’s leaked password. After stealing 100 GB of data, the attackers installed software that blocked Colonial Pipeline’s access to its IT network. Colonial Pipeline had to shut down production to stop the software spreading. This led to petrol shortages, which caused airline and freight delays and increased the price of petrol globally. |
|
2022 Costa Rica state of emergency |
In May 2022 Costa Rica’s government declared a state of emergency after malicious users got access to the government’s IT network using a leaked password. After stealing sensitive financial information, the malicious users installed software that shut down critical financial systems. This stopped the government from paying its workers and disrupted its tax and customs systems. As a result, Costa Rica’s import and export logistics collapsed, which made the government lose US$30 million per day. |
|
2022 Australian Optus data breach |
Most attacks in Australia cause data breaches, including the Optus cyber attack in 2022. In this attack, malicious users got Optus customers’ information using software that did not require authentication to access. The malicious users stole 10 million past and existing customers’ addresses and driver licence numbers. State governments were forced to reissue licences due to the heightened risk of identity theft. |
|
2022 Fire Rescue Victoria data breach |
In December 2022 Fire Rescue Victoria reported a cyber attack that impacted a number of its communications systems. On top of data breaches of current and previous staff’s personal information, data about people who had applied for positions was also leaked. The cyber attack caused an outage of Fire Rescue Victoria’s computer dispatch system and phone lines. This left firefighters having to rely on alerts about emergencies directly from their mobile phones or radio messages. |
|
2023 Tasmanian Government data breach |
In April 2023 the Tasmanian Government announced that 16,000 documents had been leaked online due to a cyber attack on its third-party file transfer system. This attack targeted the Tasmanian Department for Education, Children and Young People. Information about students’ names, addresses and their families’ bank details was compromised. |
Source: VAGO from public media.
Who carries out cyber attacks?
There are various types of malicious users with different motivations for carrying out a cyber attack:
|
Malicious users |
Common motivation |
|---|---|
|
Nation-states |
Geopolitical |
|
Cybercriminals |
Profit |
|
Hacktivists |
Ideological |
|
Terrorist groups |
Ideological violence |
|
Thrill-seekers |
Satisfaction |
|
Insider threats |
Discontent |
Cybersecurity
What is cybersecurity?
An agency’s cybersecurity or cybersecurity posture is its ability to identify, protect, detect and respond to cyber attacks.
Cybersecurity is different from IT or data security. Figure 2 shows the differences.
Figure 2: Differences between cybersecurity, information security and IT security
Source: VAGO based on information from industry standards.
Improving cybersecurity
As Figure 3 shows, an agency can improve its cybersecurity by having strong:
- technical controls, including system configurations
- administrative controls, including frameworks, policies, guidelines and processes
- physical controls, which are tangible methods of preventing or detecting unauthorised access to a system.
Figure 3: Types of cybersecurity controls
Source: VAGO based on information from industry standards.
Without correct system configurations, an agency cannot reduce its cybersecurity risks, despite having good administrative and physical controls.
Well-configured technical controls achieve a balance of security and productivity.
This audit focuses on agencies’ technical controls – their system configurations for the Microsoft 365 environment.
Compliance and security
There are 2 important concepts for measuring technical controls – compliance and security, which Figure 4 shows.
Compliance focuses on meeting industry standards. Security goes beyond compliance. It is about implementing measures to reduce the risks of cyber attacks to an acceptable level.
Figure 4: Compliance vs. security
Source: VAGO based on information from industry standards.
This audit focuses on how agencies’ technical controls align with best practice compliance.
How the cloud improves cybersecurity
The fourth industrial revolution is the next phase of digitising the workforce. It is driven by improvements in data, connectivity and technology.
Cloud computing is essential to the fourth industrial revolution. It allowed Victorian public sector agencies to work remotely during the COVID-19 pandemic.
The cloud can improve an agency’s cybersecurity if it is configured effectively. This is because it:
- shifts cybersecurity responsibilities to cloud providers, which frees up agencies’ resources
- leverages the cloud provider’s security capabilities for extra protection
- uses information from cloud providers to improve detection and response times to cyber threats.
Figure 5 shows the allocation of responsibilities for the 4 main cloud security types.
Figure 5: Shared responsibility model
| Application configuration | On premises | IaaS | PaaS | SaaS |
|---|---|---|---|---|
| Application configuration | ||||
| Identity and access controls | ||||
| Application data storage | ||||
| Application | ||||
| Operating system | ||||
| Network flow controls | ||||
| Host infrastructure | ||||
| Physical security |
| Customer is predominately responsible for security | |
| Both customer and cloud service have security responsibilities | |
| Cloud service is fully responsible for security |
Note: IaaS stands for infrastructure as a service, PaaS stands for platform as a service, and SaaS stands for software as a service.
Source: VAGO based on the Australian Cyber Security Centre’s 2022 cloud security guidance.
Cloud service providers
Common cloud service providers include:
- Microsoft 365 and Microsoft Azure
- Amazon Web Services
- Google Cloud Platform.
The cloud
The cloud is when a service provider supplies software, data storage and other services over the internet.
The cloud is more economical, effective and efficient compared to traditional computing, which relies on in house servers and databases.
Zero trust
Zero trust is the concept of not trusting anything inside or outside an agency’s network.
Under a zero trust model, an agency’s IT system explicitly verifies users and devices before they can access resources. Zero trust creates a secure environment that protects against unauthorised access to sensitive data.
The zero trust model applies to 6 key pillars, which Figure 6 shows.
Figure 6: The 6 pillars of zero trust
Source: VAGO based on information from Microsoft.
This audit looks at identity and device controls.
Relevant frameworks, roles and responsibilities
Cybersecurity standards and frameworks
Many globally recognised organisations have published standards and frameworks for improving cybersecurity. These include:
|
Organisation |
Standards or frameworks |
|---|---|
|
Australian Cyber Security Centre |
|
|
Center for Internet Security (CIS) |
CIS Critical Security Controls |
|
Defence Information Systems Agency (DISA) |
Security technical implementation guides |
|
Microsoft |
Microsoft Cloud Security Benchmark documentation (MCSB) |
|
National Institute of Standards and Technology |
NIST Special Publication 800-53: Security and Privacy Controls for Information Systems and Organizations |
|
Office of the Victorian Information Commissioner |
|
|
Payment Card Industry Security Standards Council |
Payment Card Industry Data Security Standard |
These standards and frameworks are comprehensive. But they have a lot of overlap and all point to similar technical configurations.
Organisations have mapped some of the similarities and differences between the standards. However, understanding the dynamics between each standard and identifying which controls to implement can require additional effort and costs for agencies.
Microsoft’s MCSB aims to harmonise the already published standards and frameworks to provide a single, comprehensive controls framework for Microsoft 365 products.
The National Office of Cyber Security
In December 2022 the Australian Government announced it is developing the 2023–2030 Australian Cyber Security Strategy. The strategy will aim to make Australia the most cyber-secure nation by 2030. It has led to the Australian Government setting up the National Office of Cyber Security.
The Australian Government has also appointed a coordinator in June 2023 who is responsible for improving Australia’s cybersecurity and resilience.
Agencies who have a role in cybersecurity in the Victorian public sector
A number of entities play a role in improving cybersecurity for the Victorian public sector, including:
|
|
Is responsible for … |
And it released … |
|---|---|---|
|
The Victorian Government |
setting out the government’s digital vision and ambition and direction for agencies to realise it |
Victorian Government Digital Strategy 2021–2026. |
|
Digital Victoria (part of the Department of Government Services) |
supporting the Victorian public sector’s digital transformation |
|
|
The Office of the Victorian Information Commissioner |
being the primary regulator and a source of independent advice to the community and Victorian Government about how the public sector collects, uses and discloses information |
|
|
Digital Health (part of the Department of Health) |
overseeing the health sector’s cybersecurity by working closely with the Victorian Managed Insurance Authority |
a health sector cybersecurity assessment tool in 2018. |
2. Effectiveness of identity and device controls
Agencies are not adequately prepared to prevent cyber attacks. This is because they have not correctly configured all of their Microsoft 365 cloud-based identity and device controls.
Why identity and device controls are important
Identity and device controls are 2 pillars of the zero trust model. These controls help an agency:
- make sure only explicitly verified users and devices can access its systems
- meet relevant compliance frameworks and standards.
Without strong identity and device controls, agencies are more at risk of cyber attacks.
Well-configured controls achieve a balance between productivity, or how quickly a person can access the resources they need, and cybersecurity.
For example, passwordless authentication:
- removes the need for users to remember and input different passwords
- is more secure, as passwords can be guessed.
This improves productivity because there are fewer prompts to input passwords for users.
Effective identity and device controls
We developed a list of best-practice compliance controls for identity and devices. We assessed agencies against this list. The list focuses on technical controls, not physical or administrative controls.
The list does not include all applicable identity and device controls. We selected these controls based on:
- relevant frameworks and standards
- implementation guidance from cloud computing product providers.
We list these frameworks, standards and guidance in Section 1.
Our list can help agencies identify gaps in how they manage their identity and device controls.
We gave each agency a personalised management letter with specific findings about its controls.
Agencies do not have fully effective Microsoft 365 cloud-based identity controls
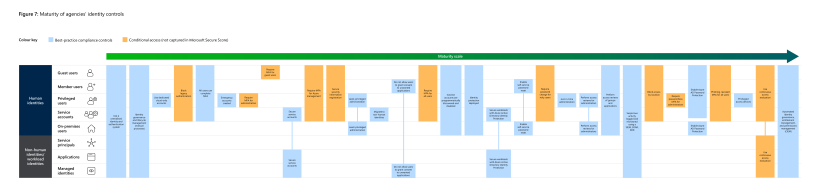
Identity controls
We assessed 33 identity controls, which Figure 7 shows.
All audited agencies can improve their cybersecurity by correcting the configuration of their identity controls.
Types of users
Agencies need to apply different identity controls depending on the user type because of their varying risks.
Common types of users include:
|
User type |
Description |
|---|---|
|
Guest user |
A user who is outside of an agency |
|
Member user |
A user who is part of an agency |
|
Privileged user |
A user who is part of an agency and has access to more functions than a standard user |
For example, privileged users can perform security-relevant functions, so agencies need to apply more controls for these users.
Figure 7: Maturity of agencies’ identity controls
Note: Download a PDF copy of Figure 7.
See Appendix B for full spelling of acronyms. As we assessed agencies' Microsoft 365 controls, the maturity model uses language from Microsoft's documentation.
Source: VAGO.
IAM systems
Agencies use an IAM system to manage users’ access to their IT systems.
A centralised IAM system:
- protects the confidentiality, integrity and availability of government information
- makes agencies more efficient. For example, when an agency creates a new user in its human resource system it triggers a creation of an account in their IAM system to match the record.
Seven out of 8 agencies have a centralised IAM system. The agency that does not have a centralised IAM system is in the final stages of implementing one.
It is positive that all audited agencies recognise the benefits of having a centralised IAM system.
Privileged access management
Agencies should use privileged access management principles to manage, control, and monitor access to important resources.
Malicious users often target weaknesses in privileged user accounts to access an agency’s network. This is because these accounts have higher-level permissions. So it is important for agencies to apply privileged access management principles to secure these accounts.
We found that 4 agencies fully use least-privileged administration to manage privileged accounts, which is good practice. The other 4 agencies are in the process of fully implementing it. However:
|
We found … |
Which … |
|---|---|
|
only 4 agencies regularly review privileged users |
involves making sure that privileged users have an appropriate access level. |
|
only 2 agencies have approval processes to activate highly privileged roles (accounts that have access to more security settings than a regular privileged role) |
involves only activating privileged roles when required. |
|
are highly privileged accounts to help agencies respond to a security emergency. |
|
only one agency uses dedicated cloud-only administration accounts |
are accounts that agencies use to change their cloud environment settings. |
|
no agencies have privileged access devices |
are devices agencies only use to do sensitive tasks. |
Authentication methods
Agencies should set strong authentication controls for their users to reduce the likelihood of cyber attacks.
All audited agencies can improve their authentication controls. For example, by configuring strong authentication methods, such as passwordless authentication, which no agency has configured yet.
MFA requires users to verify their identity using at least 2 methods before they can access an agency’s systems or documents. Only 4 agencies require MFA for all users.
According to Microsoft:
- authentication via a text message is not secure
- it is best practice is to use passwordless authentication.
Passwordless authentication is convenient for users. It can also protect an agency’s cybersecurity by letting a user access an application or IT system without entering a password or answering security questions. Instead, the user may log in with passwordless technology, such as a mobile phone authentication app, hardware security keys or biometrics.
All audited agencies can increase their authentication methods by implementing the authentication controls in Figure 7.
Case study: One agency has not set up MFA for 48 per cent of its Microsoft 365 users.
The agency told us this is because this user group can experience significant difficulties with MFA.
When we asked what the impact would likely be if this group’s accounts got compromised, the agency could not tell us. The agency confirmed that it has not conducted a comprehensive risk assessment to inform the accountable cybersecurity risk owner about:
- the likelihood and impact of the information being breached
- if the perceived ‘difficulties’ outweigh the implications of the accounts being compromised.
The number and severity of cyber attacks are increasing. So agencies cannot skip a significant control only because it is difficult to implement.
Conditional access policies for identity
An agency can configure conditional access policies to continuously verify each attempt to access its network using signals, such as a user’s location, application and device types.
For example, an agency can block an account based on its login location. This is a simple conditional access policy that helps the agency identify and prevent suspicious accounts from accessing its systems from an unusual location.
Agencies with conditional access policies require users to complete an action when they need to access a resource. For example:
|
If staff log in with a device that is assigned to them and on a network that is … |
Then the staff … |
|---|---|
|
compliant |
may bypass MFA. |
|
noncompliant |
must complete MFA. |
We looked at 5 conditional access policies for identity.
Only one agency uses all these controls appropriately.
All audited agencies can improve their implementation of conditional access policies.
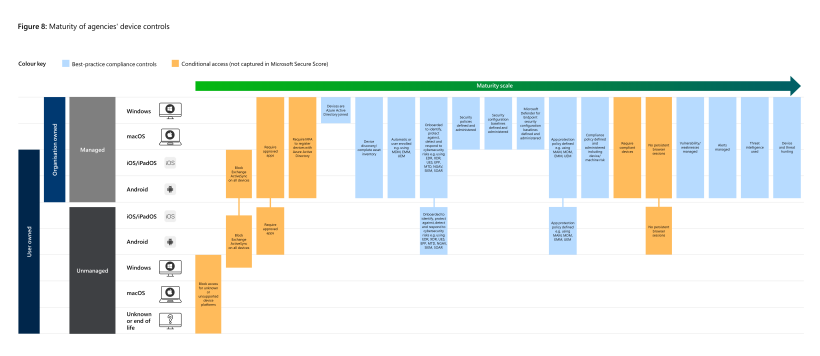
Agencies do not have fully effective Microsoft 365 cloud-based device controls
Device controls
We assessed 22 device controls, which Figure 8 shows. All audited agencies can improve their cybersecurity by correcting their configuration of device controls.
Types of devices
The different types of devices are:
|
Device type |
Description |
|---|---|
|
Workstations |
Includes desktops and laptops that can run operating systems, such as:
|
|
Mobiles |
Includes mobile phones and tablets that can run operating systems, such as:
|
Some agencies enable staff to work remotely on their own devices, which is known as bring your own device (BYOD). Agencies need to configure relevant controls to ensure these devices do not expose them to malicious users.
For example, agencies should, at a minimum, manage the applications users have in BYODs to ensure they comply. However, we found that most agencies have not focused on managing BYODs, so our findings relate to devices owned by agencies.
Figure 8: Maturity of agencies’ device controls
Note: Download a PDF copy of Figure 8.
See Appendix B for full spelling of acronyms. As we assessed agencies' Microsoft 365 controls, the maturity model uses language from Microsoft's documentation.
Source: VAGO.
Conditional access policies for devices
Similar to conditional access policies for identity, an agency can configure conditional access polices for its devices to make sure they meet certain requirements before accessing its systems.
For example, an agency might stop devices that do not have antivirus software installed from accessing its network.
To set conditional access policies for devices, agencies can:
- use a default policy issued by their cloud provider
- develop their own rules.
|
We assessed … |
Out of the 8 agencies, we found … |
|---|---|
|
5 conditional access policies for devices. |
|
|
if agencies define compliance policies and monitor device compliance status. |
|
None of the agencies have a control to block users with noncompliant devices from accessing their network. This could mean malicious users can take advantage of the vulnerabilities of these devices to access agencies’ systems.
Security configuration baselines
Security configuration baselines are minimum requirements necessary for an information system to maintain an acceptable level of risk.
Agencies, such as CIS and DISA, issue widely accepted best-practice security configurations for different cloud provider products, devices and other services.
Agencies should use best-practice security baselines but can customise some settings to suit their operating environment.
If agencies customise settings, they should clearly document any changes they have made to the best-practice baseline. This can help risk owners track and make sure they accept the consequences of any deviations.
|
We found … |
This means that … |
|---|---|
|
one agency has not considered using a security configuration baseline. |
They do not know if they have their workstations and mobiles configured in line with best practice. |
|
3 agencies have implemented a customised security configuration baseline but they have not sought approval from their risk owners. |
Their risk owners have not assessed if they accept the consequences of these deviations. |
|
of the 4 agencies that have security configuration baselines, 2 do not monitor if devices comply with these baselines. |
They do not know if their devices are configured in accordance with their security configuration baselines. |
Case study: One agency has a documented approval process for customising security configuration baselines. This is better practice.
One agency configures its devices based on Microsoft’s security configuration baseline.
The agency has deviated from the baseline in some instances so it can customise some controls. But the agency has clearly documented:
- why the recommended settings were not fit for purpose
- what changes it made
- who approved the changes.
This is an example of better practice because it shows that the agency:
- has used a best-practice baseline as its starting point
- only allows the best-practice baseline to be modified through a robust change control process.
Native cybersecurity solutions
Modern cybersecurity solutions enable agencies to prevent, detect and respond to cyber attack more effectively and efficiently. They leverage methods, such as configuring automated investigation and remediation capabilities, to reduce the time and effort security operations staff need to address a cyber attack alert.
Native cybersecurity solutions are provided by cloud computing platform providers.
We found that not all audited agencies use native cybersecurity solutions. They advised that this is because they already have other solutions that have similar functions.
However:
|
Agencies with non-native cybersecurity solutions may … |
Because … |
|---|---|
|
pay extra costs for duplicating tools |
some native solutions are already included in the agencies’ plans as part of the Victorian Government’s licensing agreement with the cloud computing platform providers. |
|
spend more time and effort analysing cybersecurity alerts |
non-native cybersecurity solutions:
|
Agencies should consider if using native solutions addresses their cybersecurity risks. If it is not the best outcome, agencies should document their rationale for using non-native solutions.
We examined if the number of devices in agencies’ device inventories aligns with their other IT system records.
We found that agencies do not keep their device inventories up to date. Only one agency knows:
- the number of devices it manages
- if it has decommissioned outdated devices.
This is because most agencies use non-native cybersecurity solutions and these solutions do not integrate different data sources automatically. Agencies need to manually reconcile records from different systems and often do not have the time and resources to do this over a large number of inventories.
Case study: One agency’s records had a difference of over 15,000 devices.
We found that one agency had over 25,900 devices recorded in its compliance management tool. But its IT device inventory only showed 10,100 devices.
The agency told us that it does not know why the records are different. It said it needs to reconcile its inventory to address the issue.
We found inaccurate asset management records at 6 of the 8 audited agencies. This is because they use a variety of cybersecurity solutions that are not integrated to enable easy reporting.
Further, while all the audited agencies have different tools to get information about their cybersecurity position, they do not always use this information to detect and monitor if unauthorised users and devices are accessing their systems.
For example, all the audited agencies have tools to identify cyber threats. But only one agency actively uses this data to regularly address its risks.
Agencies can improve their reporting on cybersecurity
Reporting on compliance and security posture
It is positive that all audited agencies:
- have assigned risk owners for their overall cybersecurity
- report emerging cybersecurity risks to relevant committees.
|
We assessed if agencies report on their … |
And we found … |
|---|---|
|
compliance against the Victorian Protective Data Security Standards |
one agency does not provide its annual attestation against the Victorian Protective Data Security Standards to its audit and risk committee. |
|
secure scores to accountable risk owners |
|
Secure scores indicate an agency’s security position in the Microsoft 365 cloud environment.
Secure scores are automatically calculated using monitoring technology that scans an agency’s environment. However, if an agency uses a third-party solution or an alternative mitigation method, the scores may not accurately reflect if a control has been adequately set up.
Of the 8 audited agencies, each agency implemented an average of 180 out of 1,072 (17 per cent) controls using third-party solutions and alternative mitigation methods.
This means that:
- the reported secure scores may not accurately reflect agencies’ true security posture
- agencies cannot solely rely on their secure scores to monitor their security position. Agencies need to confirm if their controls that use third-party and alternative mitigation methods have been set up properly.
Not all audited agencies understand and oversee cybersecurity services delivered by third-party providers
Why clear roles and responsibilities are important
An agency can manage cybersecurity risks in-house or use a third-party provider to deliver some services.
But the agency is accountable for its overall cybersecurity risks. This is because an agency cannot delegate accountability to a third-party service provider. This means:
|
An agency can … |
This is called a … |
But … |
|---|---|---|
|
rely on a cloud service provider to provide a system, such as a shared Microsoft 365 tenancy, to store and transmit data. |
shared service |
The cloud service provider determines and configures the controls for the system. Before using the system, the agency needs to make sure the controls for the system are sufficient to address cybersecurity risks. As a user of the system, the agency needs to periodically assess:
|
|
use a provider to help it implement and manage some controls. |
managed service |
the agency needs to determine and oversee the controls set up by the third-party service provider. |
Cenitex’s role as a service provider
Cenitex manages a suite of Microsoft 365 products. Many government agencies use and share these products and services.
Cenitex can play different roles for these products depending on how agencies engage with it.
When Cenitex is the cloud service provider under the shared service arrangement:
- Cenitex is the owner of the shared products and services so it is responsible for determining and configuring cybersecurity controls for the Microsoft 365 tenancy
- agencies are users, not owners, of these products and are only responsible for their data in the Microsoft 365 products.
Cenitex maintains a controls library. Its clients can ask to see this library and any associated security settings that relate to them. Agencies can use this information to make sure the controls are:
- appropriate for their risk profiles and appetite
- operating effectively.
Each year Cenitex gives its clients a report from an external assurance provider about the effectiveness of the controls it manages.
Cenitex’s shared services and products
Agencies are not clear about their security roles and responsibilities under their shared service arrangement with Cenitex.
For example, agencies say they are the owners of the shared Microsoft 365 tenancy and should be able to determine and set up controls.
But the Information Security Manual says that a user’s roles and responsibilities under a shared tenancy should be to:
- periodically review if controls set up in the tenancy by Cenitex meet its cybersecurity requirements
- identify if it needs to implement additional controls to address any identified gaps and assess if:
- these controls can be implemented in the tenancy by Cenitex
- it needs to set up its own controls to mitigate the cybersecurity risks.
If these options are not possible, agencies should consider other suitable arrangements.
If Cenitex and its clients are unclear on who is responsible for determining, implementing and overseeing controls, agencies may not be able to adequately manage their cybersecurity risks.
3. Whole-of-government approach to cybersecurity
The public sector does not use its size and economy of scale to address cybersecurity risks in a coordinated way. Agencies have recognised the need to establish a whole of government approach but need to do more to improve the public sector’s cybersecurity.
Agencies lack a coordinated approach to address cybersecurity risks
Why a coordinated approach is important
As agencies move away from on-premises computing to cloud computing platforms, they are also increasingly changing their control configurations from agency-specific settings to universal uniformed ones. This means that the identity and device control options for agencies will become well defined and near identical. This can help agencies configure controls easily with reduced effort.
Agencies recognise that:
- cybersecurity skills are distinct from general IT skills
- preventing, detecting and responding to cyber attacks requires a multidisciplinary team with expertise across different security functions.
The Victorian public sector has over 3,000 entities that deliver services to the public.
Without a coordinated approach, many agencies are duplicating their efforts and not using the public sector’s economy of scale to efficiently manage cybersecurity risks.
Proposed whole-of-Victorian-Government cyber operating model
Victoria’s Cyber Strategy 2021 and its 2021–2023 mission delivery plans recognise the need to:
- set up a whole-of-Victorian-Government operating model to improve how the public sector manages cybersecurity risks
- encourage more agencies to use baseline controls and improve their cybersecurity skills
- build a cyber hubs model to improve the sector’s governance, technology and how it manages resources. A central Victorian Government cybersecurity defence centre would support these hubs.
In August 2022 Digital Victoria issued the Victorian Government Office 365 Security Guidance as part of Victoria’s Cyber Strategy 2021 and mission delivery plans.
This is Digital Victoria’s first effort at leading a whole-of-government approach to address cybersecurity risks.
Digital Victoria also asked agencies to voluntarily share their secure score data with it so it could:
- analyse agencies’ cybersecurity
- identify which agencies need extra support
- identify what areas agencies need further training in.
However, not all agencies agreed to share their data. This is because Digital Victoria has no legal authority to issue mandatory guidance and request information.
Although 150 agencies agreed to participate in the program, only 40 agencies voluntarily shared their data. As a result, Digital Victoria could only analyse data of 40 agencies, or 27 per cent of participating agencies.
This means Digital Victoria:
- does not have full visibility of agencies' cybersecurity data
- cannot identify systemic issues or concerns across the sector.
This may affect Digital Victoria's ability to deliver the whole-of-government cyber operating model.
Using centralised SOCs
Under Victoria's Cyber Strategy 2021 and its 2021–2023 mission delivery plans, Digital Victoria aims to set up centralised SOCs for agencies to use.
A SOC is an in-house or outsourced team of IT security professionals that monitors an agency's IT infrastructure 24/7 to detect and respond to cyber attacks.
The health sector set up its SOC in 2020. This is a good example of agencies detecting and responding to cybersecurity threats using a centralised solution.
Case study: The health sector’s SOC helps health agencies monitor, detect and respond to cybersecurity threats.
In 2020 the former Department of Health and Human Services (now the Department of Health) helped set up a sector-wide SOC for health agencies.
The department oversees the provider who runs the SOC. It paid to set up the SOC and the first 3 years of ongoing management fees. The agencies that use it pay the ongoing management fees.
Over 120 health service providers, or 98 per cent, use the SOC. They receive sector-wide warnings and incident alerts to help them address threats.
The department holds monthly meetings with the SOC provider to discuss key performance and alert trends.
This arrangement helps the department monitor, identify and quickly respond to issues or threats that affect the entire sector.
Similarly, the Department of Premier and Cabinet and the former Department of Environment, Land, Water and Planning (now the Department of Energy, Environment and Climate Action) set up a water sector SOC in 2022.
As of March 2023, 17 water entities have planned to join the SOC. As of March 2023, 2 of these entities have finished the onboarding process. The rest are due to complete it by the end of 2024.
However, the current SOC arrangement does not provide services for protecting against cyber attacks. This duplicates effort because individual entities need to deliver this function independently.
It is often challenging for individual agencies to have the necessary resources and scale to establish cybersecurity teams with up-to-date knowledge and skills. This can expose agencies to high cybersecurity risks.
Appendix A: Submissions and comments
Download a PDF copy of Appendix A: Submissions and comments.
Appendix B: Abbreviations, acronyms and glossary
Download a PDF copy of Appendix B: Abbreviations, acronyms and glossary.
Appendix C: Audit scope and method
Download a PDF copy of Appendix C: Audit scope and method.